cybersecurity advisory blog

The Myth of “Mature” Security Programs in Mid-Sized Companies
Most mid-sized companies think their security program is “mature.”
In reality, many are optimized for audits—not real risk.


Do You Have Executive-Level Security Leadership?
Many growing companies invest in security tools and compliance efforts but still lack true executive-level security leadership. Without someone responsible for aligning cybersecurity with business strategy, organizations often operate reactively—focusing on audits, tools, and technical tasks rather than managing security as a business risk. This article explores why executive security leadership matters and how organizations can bridge the gap.

Most Breaches Happen Because the Basics Fail
Most cyberattacks don’t rely on advanced techniques—they exploit basic failures. Weak passwords, missing patches, poor access controls, and lack of monitoring create easy entry points that attackers consistently take advantage of. The real risk isn’t sophistication—it’s inconsistency in executing the fundamentals.

Risk-Based Security vs. Checkbox Compliance: Why the Difference Matters
Most organizations believe they’re secure because they’re compliant. In reality, compliance only proves you’ve met a baseline—not that you’ve addressed what actually puts your business at risk.
Risk-based security shifts the focus from “checking boxes” to protecting what matters most: your data, your operations, and your customers. It prioritizes real-world threats, aligns security with business goals, and ensures every control has a purpose.
If your security program is driven by audits instead of risk, you may be doing a lot of work—without meaningfully reducing exposure.
Why Cybersecurity Audits Fail — And How to Avoid the Most Common Mistakes
Cybersecurity audits are not inherently difficult. What makes them painful — and often unsuccessful — is the way organizations prepare for them. Across SOC 2, HIPAA, HITRUST, ISO 27001, PCI, and NIST-based assessments, the same patterns appear repeatedly. Most audit failures are not technical failures. They are governance, process, and execution failures.

Why Most SMB Companies Don’t Need a Full-Time CISO
What SMBs typically need is experienced security leadership, on demand, paired with a pragmatic, risk-based program—not a seven-figure executive hire.
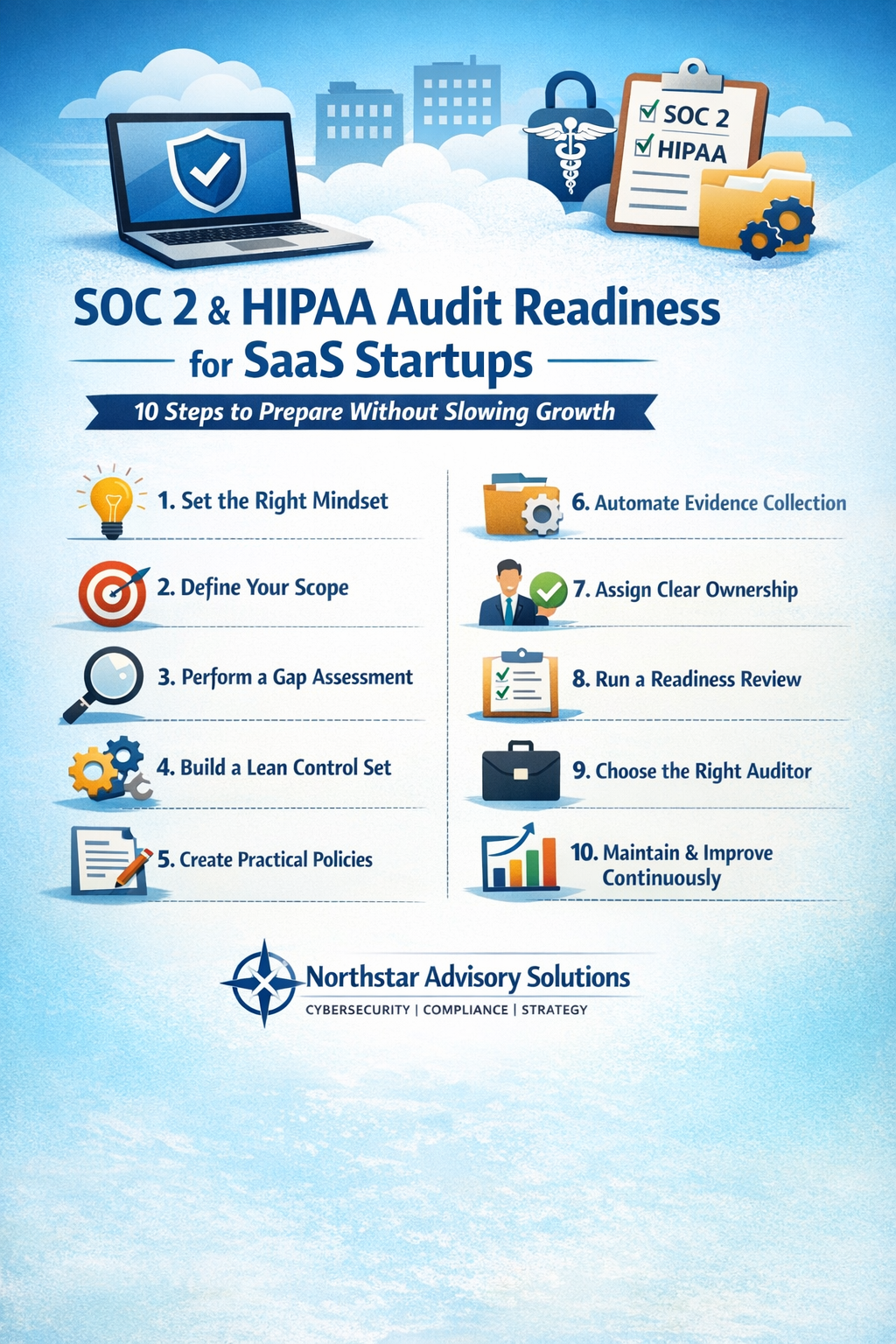
How SaaS Startups Can Prepare for SOC 2 and HIPAA Audits (Without Slowing Growth)
For many SaaS startups, SOC 2 and HIPAA audits feel like unavoidable hurdles on the path to scale. Customers demand assurance. Partners require proof. Sales cycles increasingly depend on it.

Beyond the Checkbox: Rethinking Cybersecurity in Healthcare
In healthcare, cybersecurity isn’t just a technical challenge—it’s a human one. The stakes are high: patient safety, regulatory compliance, and organizational trust all hinge on how well we protect sensitive data and critical systems. Yet too often, security programs fall into the trap of becoming a checklist exercise—focused on compliance artifacts rather than meaningful risk reduction.
Cyber Risks Are Everywhere
As organizations continue to adopt cloud services, AI tools, and third-party platforms, the line between “our risk” and “their risk” keeps getting thinner. A single vendor outage, misconfiguration, or access issue can ripple quickly into business disruption, data exposure, or compliance challenges.

AI is Enhancing Cybersecurity
Across many organizations, AI is helping security teams move faster by spotting patterns humans can’t easily see—whether that’s identifying suspicious behavior, prioritizing alerts, or reducing noise so teams can focus on what actually matters. It’s also improving response by automating routine actions and helping analysts get ahead of threats instead of reacting after the fact.
